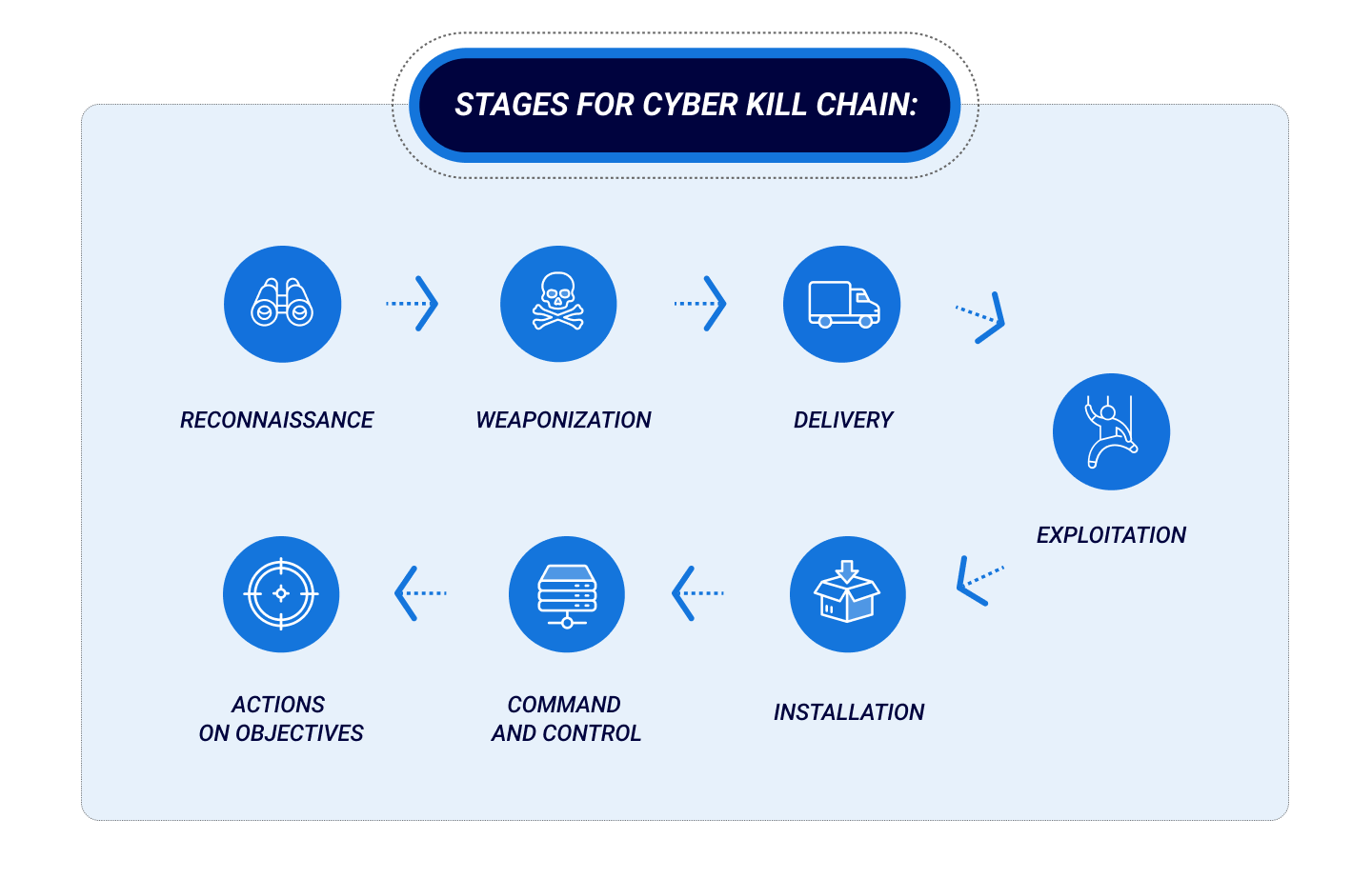
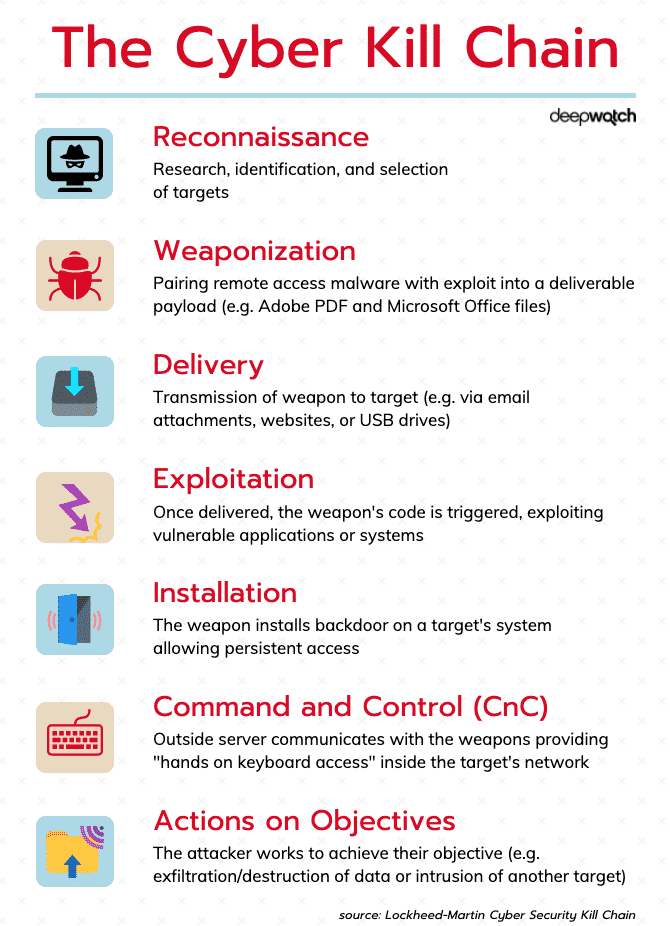
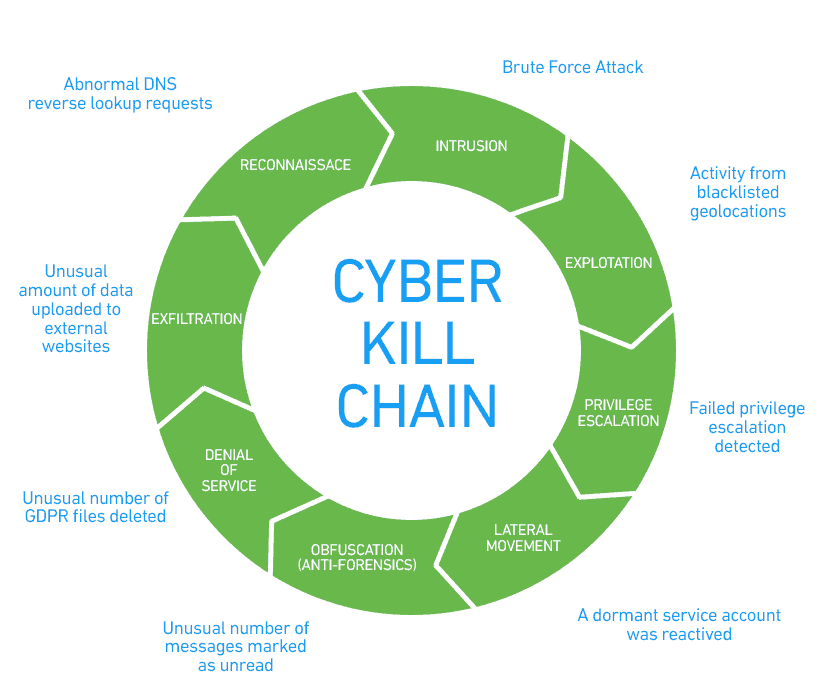
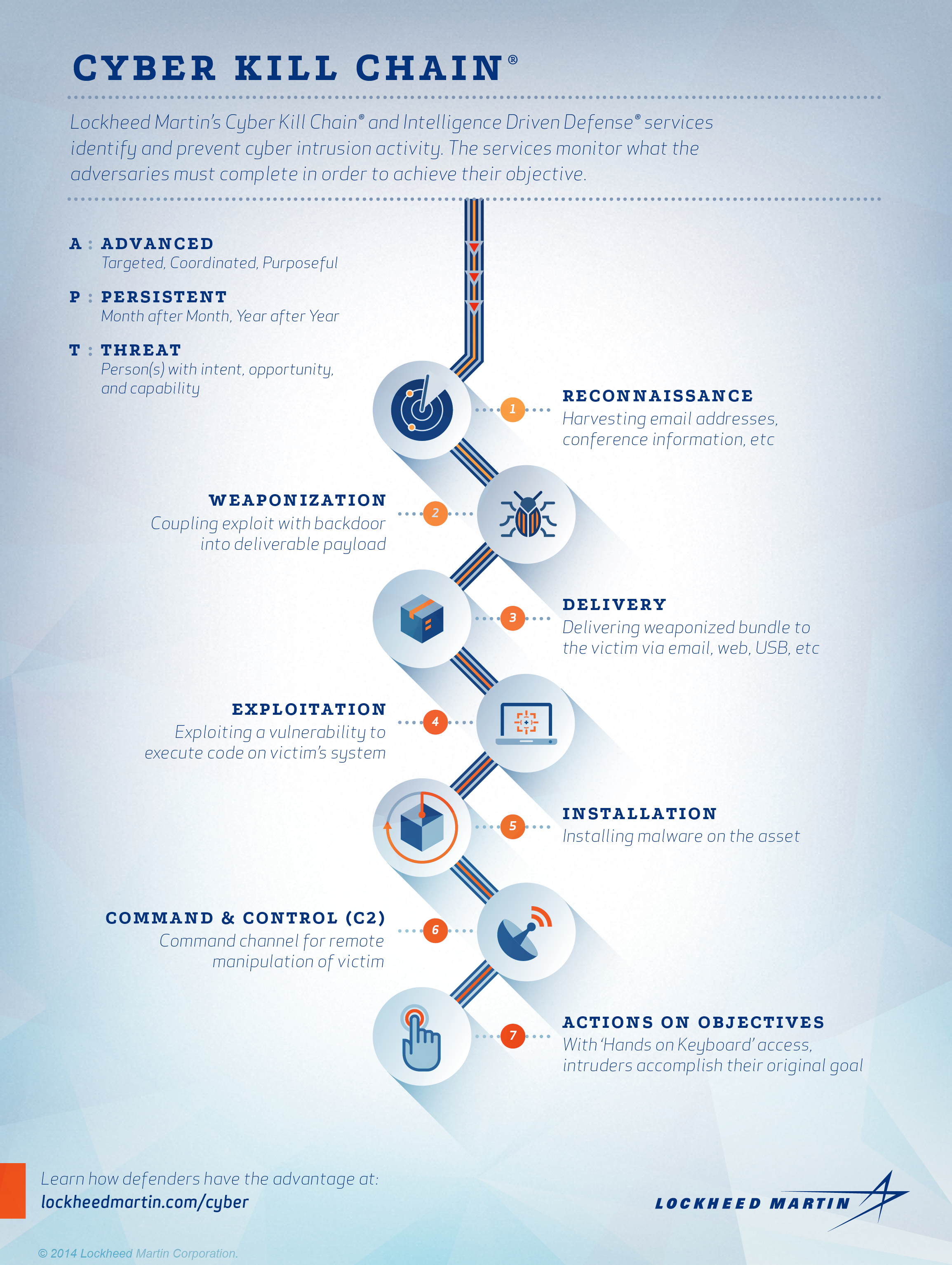
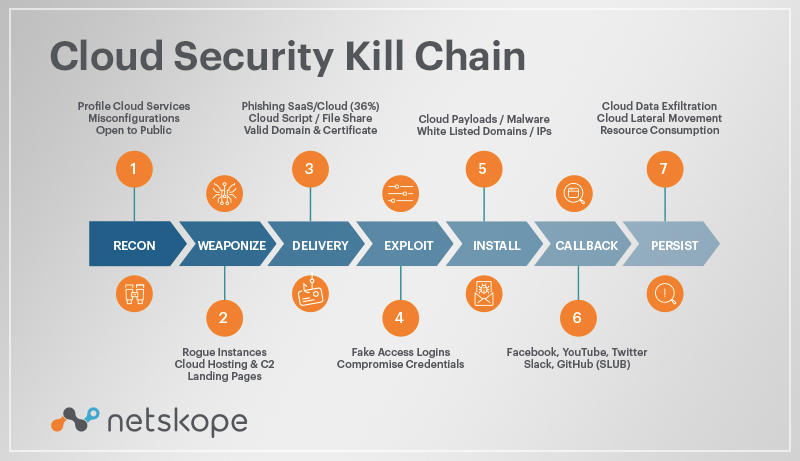
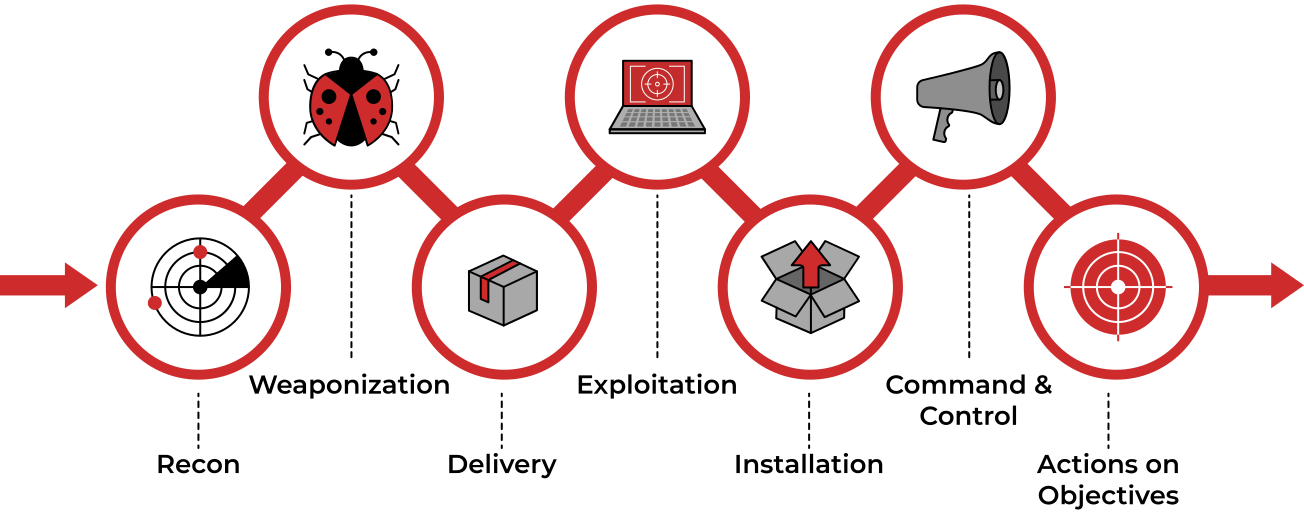
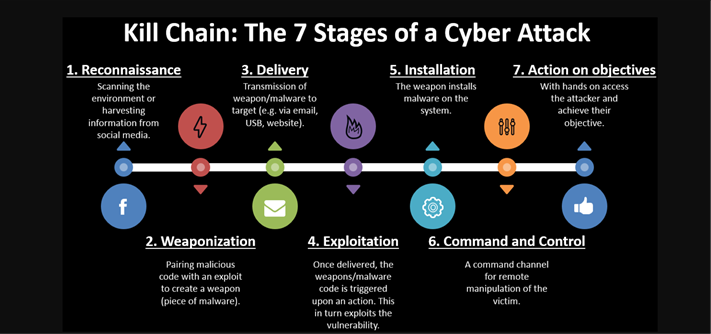
EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber
Is the Cyber Kill Chain Model the Ultimate Solution to Rising Ransomware Attacks? - United States Cybersecurity Magazine
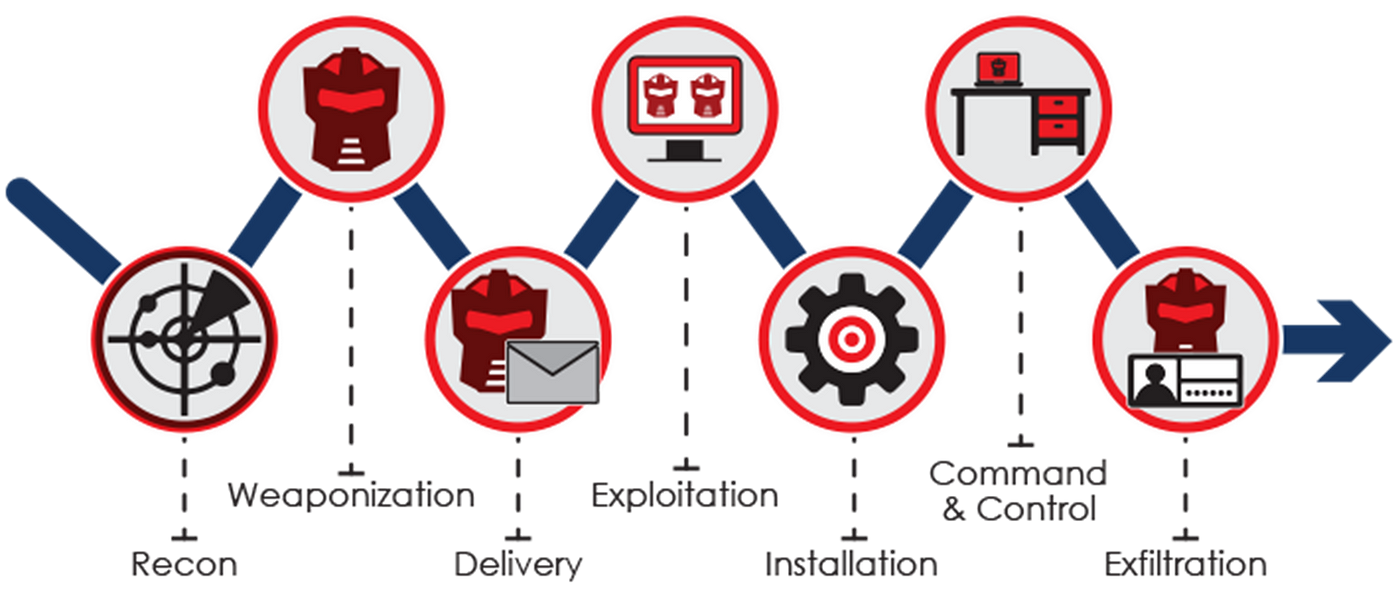
![PDF] Kill Chain for Industrial Control System | Semantic Scholar PDF] Kill Chain for Industrial Control System | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/824c717392e285cd8cc637085ef7bc982c7e2bf7/3-Figure2-1.png)